Webinar on Demand: Supporting your critical end-of-life Windows 2003 Application Servers
Supporting your critical end-of-life Windows 2003 Application Servers.
Are Windows 2003 servers causing you sleepless nights?
At APPtechnology we have been working with Droplet Computing for several years to help solve the problem of legacy applications in the desktop space running on Windows NT, Windows Vista or Windows 7, helping to isolate software with no upgrade path so that it can be used securely and indefinitely.
Until recently, Droplet containerisation has focused on securing outdated desktop applications. But if you've been suffering sleepless nights because of a Windows 2003 server application that you know to be vulnerable, you'll be relieved to learn that Droplet has now been extended to provide support for back-end servers.
Complex client-server applications running old code can now be deployed securely to the cloud, allowing you to move ahead with long-overdue server migrations being held up because of legacy servers - and finally get a good night's rest.
As COO Barry Daniels explains in this 26 minute, on-demand webinar video, Droplet's worldwide-patented containers provide three key benefits: security, compatibility and compliance.
What is Droplet Computing?
Droplet should not be confused with Docker, which is not used anywhere in the Droplet technology. Docker containers are intended for distributing modern applications to control the cost of cloud services. Droplet containers, on the other hand, are used to isolate legacy applications to give them the freedom to persist, protecting them from zero-day threats.
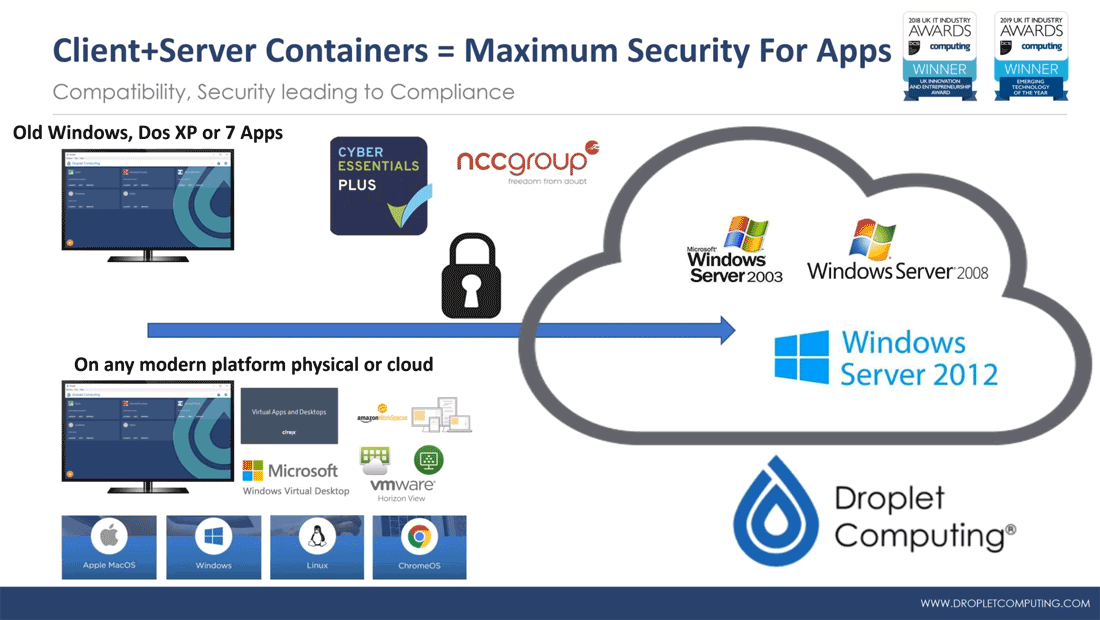
And once isolated they can be run across multiple platforms and in the cloud.
A lot of the high-profile breaches that have happened in recent times have been the result of legacy systems within infrastructures. Droplet protects applications, both on the client and server side, from those attacks.
Introducing Droplet Server Containers
Droplet's server containers serve the same purpose as the desktop containers, offering server persistence across a multitude of different systems, particularly vSphere and Microsoft Azure, but also AWS and even a bare metal implementation of the Droplet virtual appliance. Whatever your original server-side software, it can be run safely and securely in a container bubble - along with all of its dependencies - without the need for any modifications.
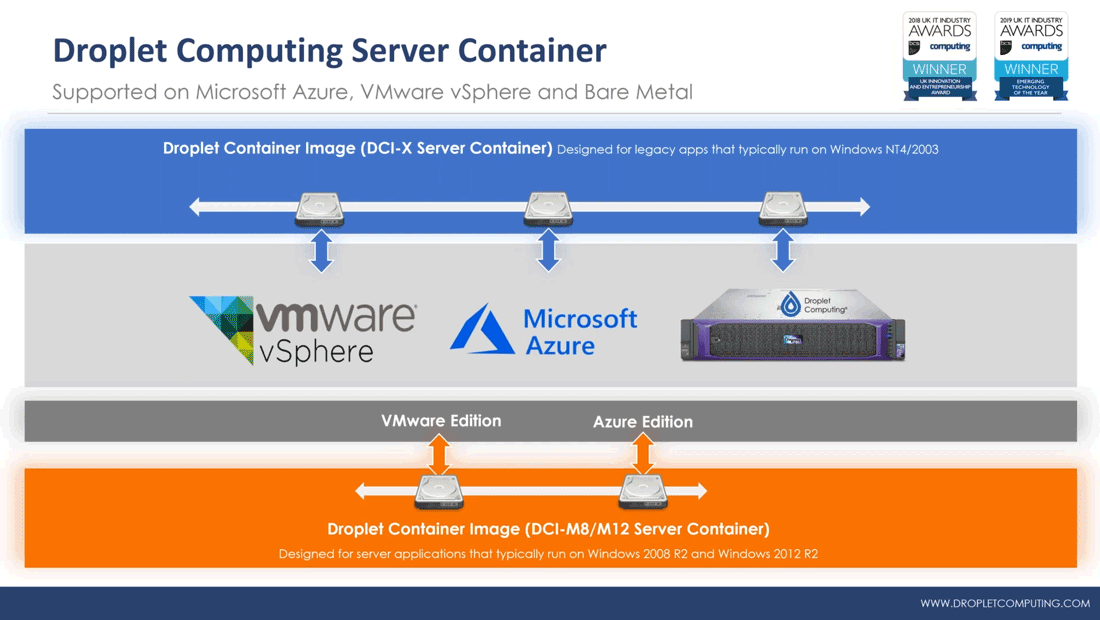
The server container does not allow any inbound traffic except the traffic that comes from the client-side container, which means absolutely no risk and can be part of your Cyber Essentials compliance strategy. The client-side container is completely invisible to the rest of the network, so it's safe to run , for example, an outdated version of Internet Explorer without fear of exploitation.
Droplet in Action
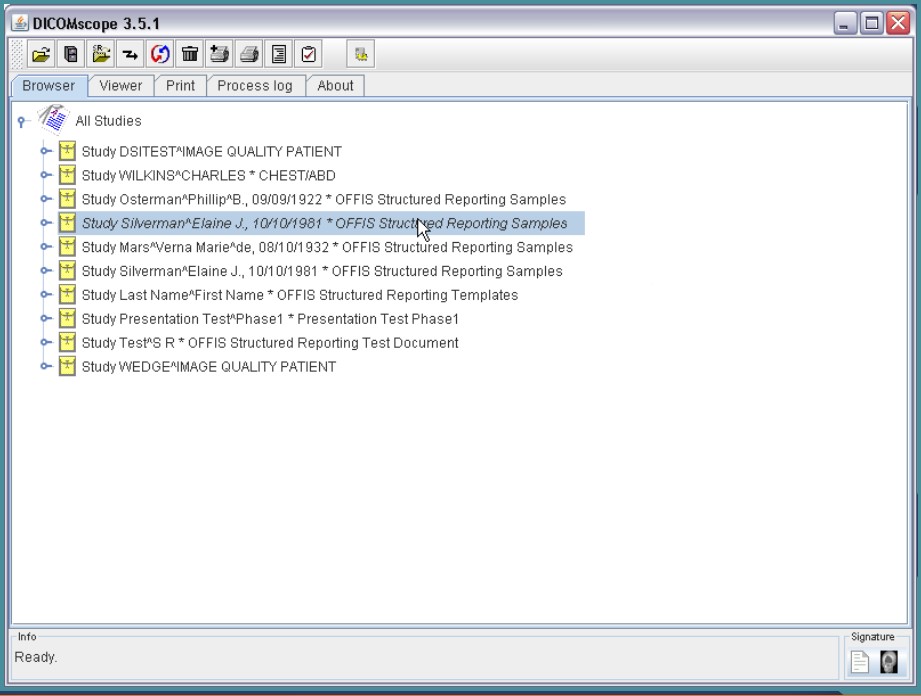
In this webinar, Michelle Laverick gives you a whistle-stop Droplet client-server containerisation tour in which she demonstrates how Droplet Computing can
- convert an exact copy of an existing virtual machine to the Droplet format
- create a secure connection between a client-side container and a server-side container
securely connect an outdated browser (IE8) to an outdated web server (IIS6) - deploy a container as a virtual appliance using VMware's OVF and OVA formats
- create a bridge to link the network adapters of the appliance to a vSphere network infrastructure
- flexibly manage storage in a SAN system using tools recognisable to network administrators familiar with VMware vMotion or Hyper-V Live Migration
- allow administrators to log on to a legacy Windows Server seamlessly, without any change to their nework security permissions
- and much more

Seamless Windows remote desktop access
FREE WEBINAR available on demand
APPtechnology and Droplet will show you how you can safely support your legacy Microsoft Server 2003 and 2008 application server workloads for delivery across multi-platform infrastructures on physical, virtual or public cloud platforms.